
March 22, 2025
31 students attended the teach-in and learned about developing security plans, safe tools to use online as well as how this information could be used at the 5Cs.

On March 3, 31 students attended a teach-in at the Motley coffeehouse on defending against surveillance for political organizing by the Electronic Frontier Foundation (EFF) and hosted by the Prison Abolition Collective. The teach-in focused on the process of developing contextual security plans, introduced trustworthy tools to use online, went over how encryption works and answered questions about how this information could be used for protesting at the 5Cs.
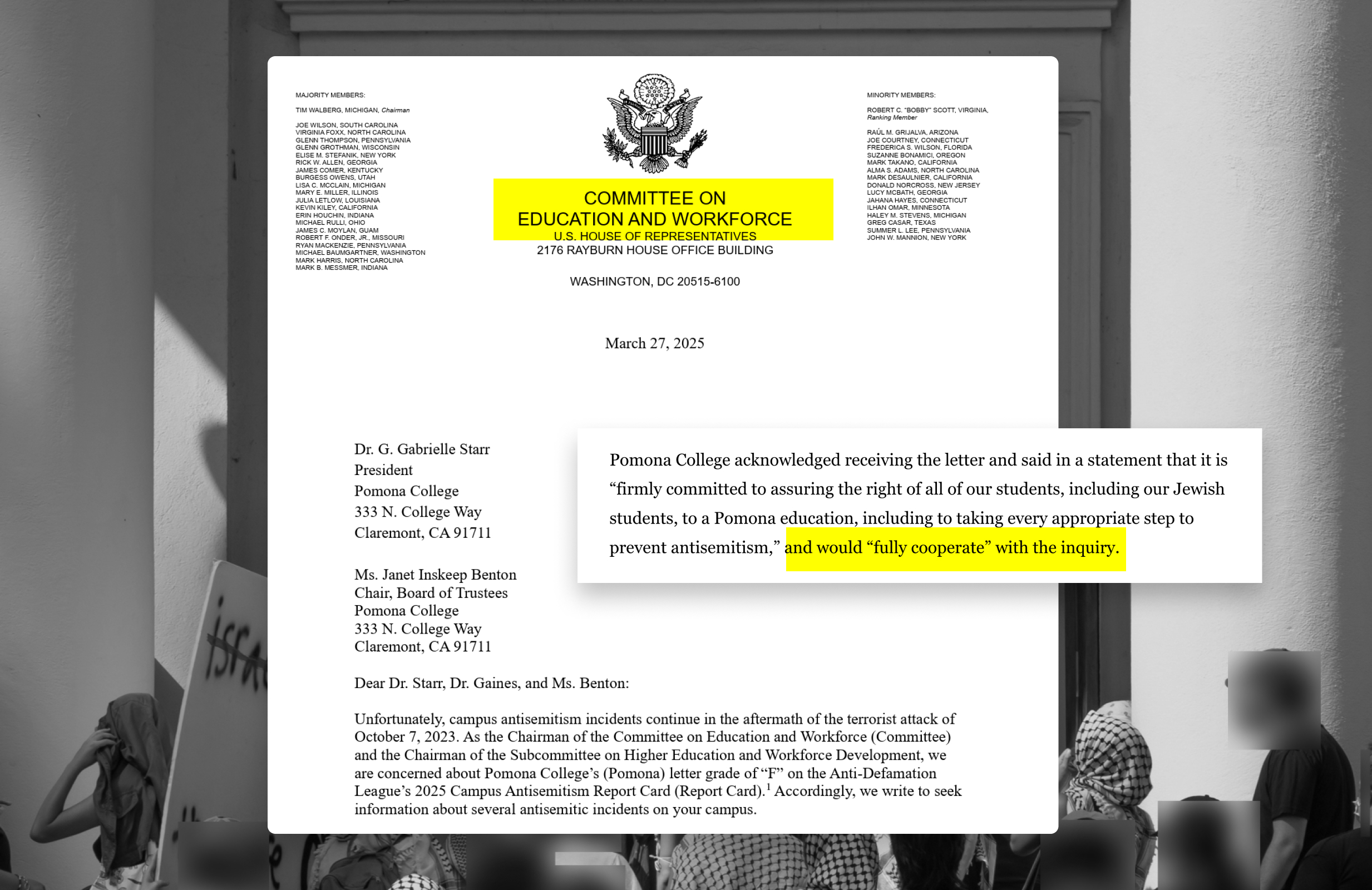
In light of increased repression from the Claremont Colleges, including the identification of students inside Carnegie Hall through Wi-Fi tracking during the Oct. 7 building takeover, the teach-in helped provide knowledge about digital security for protestors and students concerned about surveillance.
The main speaker at the event was Thorin Klosowski, Security and Privacy Activist for the EFF. Klosowski began the talk by passing out a valuable one-pager with summarized digital security advice: eff.org/r.nf9h.
He then introduced the EFF which is composed of three branches: the legal team, the technology team and the activism team. These branches have been working together for over 30 years fighting for increased digital rights, including multiple current campaigns fighting for reproductive justice.
Security fundamentals
The first thing Klosowski outlined was the basics of digital security fundamentals. He said that a general guideline for maintaining digital security includes: using unique passwords everywhere, enabling two-factor authentication when applicable, using device encryption on computers and phones, being mindful of social media presence and mitigating the threat of doxxing.
He explained how using a unique password everywhere as well as a password manager helps mitigate the threat of data breaches.
Two-factor authentication helps provide security against phishing attempts by putting a second blocker between the phishing attempt and the device, making the account much harder to access.
Similarly, Klosowski said that using device encryption — such as a phone password, touch ID and face ID — ensures that “[even] if they’re a very good hacker, they’re not gonna be able to get into [your device] without knowing your password.”
Being mindful of social media presence is another step Klosowski outlined as especially important to mitigate the threat of doxxing, especially as police continue to use surveillance of social media posts as a tool to repress Palestine solidarity protests.
The Trump administration’s recent detention and attempted deportation of a postdoctoral fellow at Georgetown, Badar Khan Suri, for his personal views on Palestine, found through his social media where he was allegedly “promoting antisemitism” is another example of the danger of posting Palestine solidarity content online.
While Klosowski acknowledged the use of social media as an organizing tool, he emphasized finding a balance between posting online and protecting your online presence.
“Security planning” rather than “threat modeling”
Klosowski then moved on to what people should be thinking about on a day-to-day basis when it comes to their digital security. He framed this using the term “security planning” instead of the more generally used term “threat modeling” because it connotes a less intense and more accessible series of steps.
“We can’t all protect everything all of the time and [trying to] do so is gonna drive us crazy,” Klosowski said.
Due to this, Klosowski showed attendees a list of relevant questions to ask themselves when making a security plan. The questions he outlined in his presentation were as follows:
He explained that these questions can help people accordingly decide what their approach to security planning will be and what information they most want to protect.
“Deciding what’s important to us and maybe what’s important in a specific situation is going to set you up for the best amount of success,” Klosowski said.
While these steps are relevant for anyone using technology, Klosowski said that an especially important question for people attending protests to think about is, “What are the consequences if I fail?”
This question is especially important given Suri’s case, as he was on a student visa, as well as the Trump administration’s detention and attempted deportation of Mahmoud Khalil, a Columbia University student, for participation in Palestine solidarity protests — despite him being a permanent US resident. Given this, protestors should think of their own documentation status as well as their families’ when imagining potential consequences.
Additionally, Klosowski made sure to add that even when focusing on technology, the risk that other people present to our protection is also important to consider.
“It’s easy to forget whenever we’re talking about digital security, but the people are often the weakest link, whether that’s in the surveillance chain or just in the communication chain,” Klosowski said.
He emphasized evaluating who you are around during protests and what they are observing as important details to keep in mind while protesting on college campuses.
Digital security tools: “a process not a purchase”
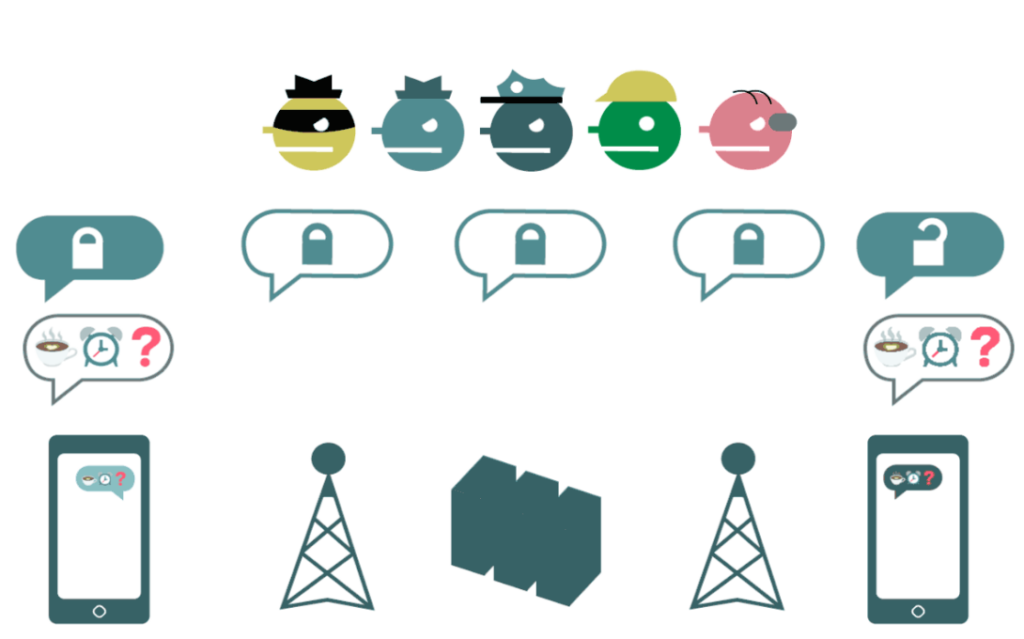
Klosowski then introduced some important tools that could be utilized in the security planning process. However, he emphasized that there was no such thing as a perfect tool and that this was a highly contextual process for each person.
Rather than thinking of a singular best tool, he advised evaluating tools with the same eye that you would give any purchase that you make, including extending beyond evaluating the tool at a current moment and instead thinking about its hypothetical future ownership.
He gave the hypothetical example of Amazon buying Slack in the future, putting in question if students would still use the site.
However, Klowsowski did also give examples of tools that are generally trustworthy to use, identifying WhatsApp and Signal as communication tools that are more secure due to how they encrypt messages.
He also identified Tor as a browser that used end-to-end-encryption and said that this was important to “access the internet with very little [trace] of a digital trail.”
Password and Bitwarden were two other examples he gave of password managers that organize all your passwords.
He also talked briefly about VPNs, highlighting how using VPNs could be helpful but shifted the risk of data surveillance over to the VPNs.
“An untrustworthy VPN would just have free reign on everything that your entire browsing history, just like an in-service provider would or network,” he said. His main recommendation was to look at Consumer Reports, who have highlighted some of the most trustworthy ones.
Klosowski finished the teach-in by outlining how end-to-end encryption for apps like Whatsapp and Signal work.
Through a regular SMS text message, he explained, anyone along the path of message delivery, including the sender, the receiver and routers in between could see the message content.
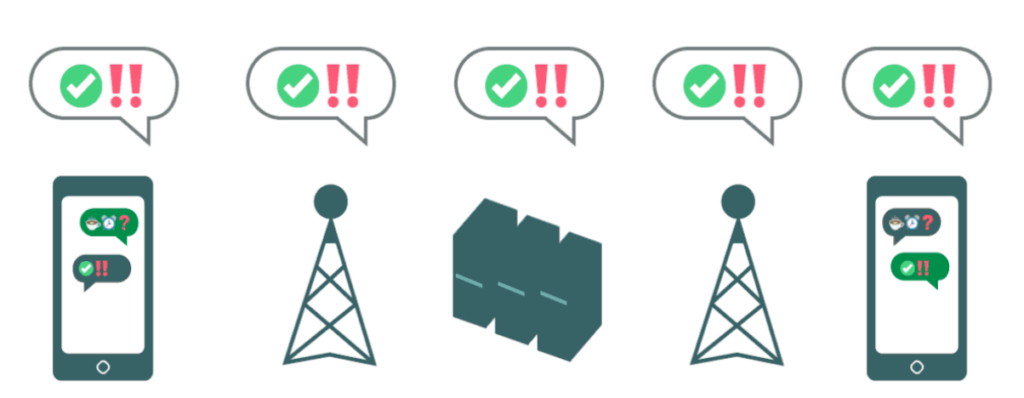
However, when using end-to-end encrypted messaging like Whatsapp or Signal, content is unreadable by anyone other than the sender and receiver.
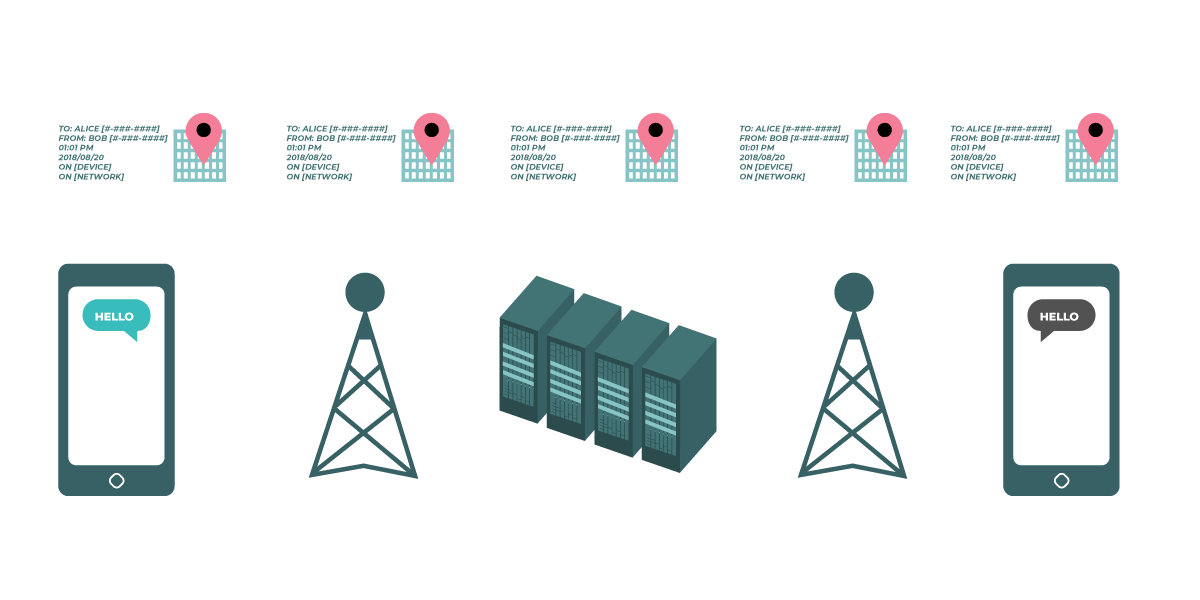
However, Klosowski added that even with encrypted messaging, metadata — who sent a message, where they were when they sent it and who they are sending it to as well as other device information — can be seen.
“Colleges are a petri dish of surveillance”
After the talk, students asked Klosowski some of their own questions about how to protect their digital security as organizers at the 5Cs.
One of the first questions asked was about how much content the school could see while using a school Wi-Fi network. In response, Klosowski said that the operator of the Wi-Fi network would know the kind of route address of the websites visited, but not the specific pages or content.
Another attendee asked about the traceability of devices while using Wi-Fi.
Klosowski explained that through a college Wi-Fi network that requires students to login with their email, the college can generally track students to a specific building. Although turning off Wi-Fi and turning your phone on airplane mode could help mitigate this, Klosowski said generally, “the answer is to leave your phone at home.”
Continuing on protest safety, he also talked about the importance of wearing generic clothes to make facial recognition more difficult.
In a response to a question about face-ID, he said that although face-ID was helpful in most circumstances to protect access to a person’s device,“if I’m ever in a situation where I feel like I might be at risk, I would turn it off.”
Despite many of these questions being specific to organizers, a main theme of the talk Klosowski made clear was that digital security was not just for high risk protestors or protest organizers. Instead, he emphasized that everybody should always be thinking about their own personal security plans.


Affinity groups

Palestine
Palestine

Undercurrents reports on labor, Palestine liberation, prison abolition and other community organizing at and around the Claremont Colleges.
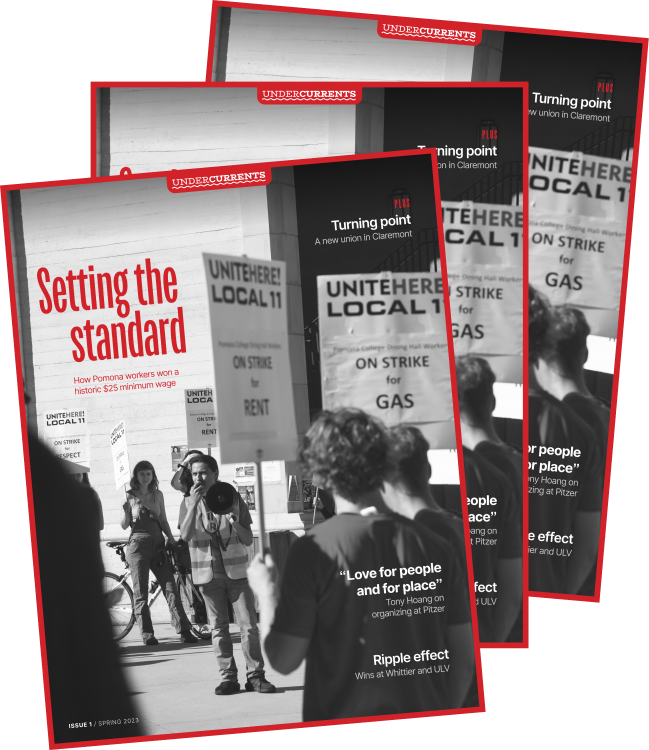
Issue 1 / Spring 2023
Setting the Standard
How Pomona workers won a historic $25 minimum wage; a new union in Claremont; Tony Hoang on organizing
Read issue 1